There’s been talk of this unauthenticated RCE vulnerability coming with a CVSS 9.9 rating but none of the technical details were publicly known until it was made public just now at the top of the hour. Simone Margaritelli discovered this vulnerability and has shared a write-up around this potentially very impactful Linux vulnerability.
This vulnerability, fortunately, doesn’t affect the Linux kernel but rather CUPS… The print server commonly used on Linux systems and other platforms.
…
From Attacking UNIX Systems via CUPS, Part I:
“A remote unauthenticated attacker can silently replace existing printers’ (or install new ones) IPP urls with a malicious one, resulting in arbitrary command execution (on the computer) when a print job is started (from that computer).”
…
This remote code execution issue can be exploited across the public Internet via a UDP packet to port 631 without needing any authentication, assuming the CUPS port is open through your router/firewall. LAN attacks are also possible via spoofing zeroconf / mDNS / DNS-SD advertisements.
Besides CUPS being used on Linux distributions, it also affects some BSDs, Oracle Solaris, Google Chrome OS, and others.
As of writing there is no Linux fix available for this high profile security issue. In the meantime it’s recommended to disable and remove the “cups-browsed” service, updating CUPS, or at least blocking all traffic to UDP port 631.

You have to make yourself so vulnerable to be affected

This is a big nothingburger because it doesn’t have a cute name, a marketing campaign, or a silly logo. /s

I had a moment of actual laughter.
I was expecting a kernel issue handling networking connections or SSH or who the fuck knows but… cups?
Printers, they ruin everything.

Loads of complex code exposed to an assumed trusted network is the model of printers. They’re going to be full of security issues.
This stuff should be sandboxed and then never, ever exposed to the Internet.

I’m always befuddled how these things end up public on the internet. (I’m not really.)
Like, it’s not like the printer is the one poking holes in your firewall while you sleep.*
*If it is, then you should feel great shame, throw away anything more complicated than a pair of dull scissors, and get a job digging holes then filling them back in.

the reporter is a real asshat, judging by their twitter.
first:
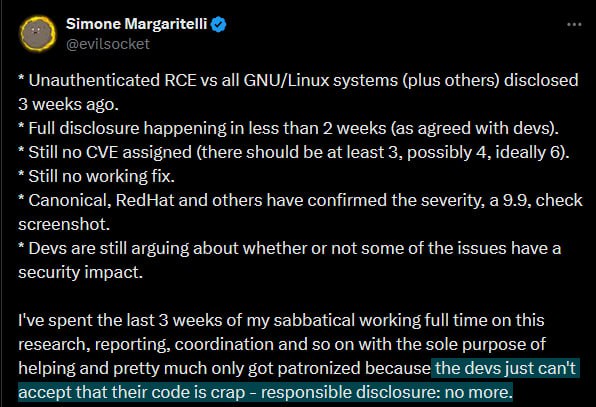

then, later:

Yep. Also claimed “it affects all GNU/Linux” while it only really does CUPS and so on.
Just alone full disclosure is a shit thing to do. Do not even mention the part where it was intended as a responsible disclosure.

Ya I was worried this was going to affect something like OpenWRT and a lot of shit was about to get fucked over. CUPS? 99.9% of people are gonna have that port closed on their router. Sure this is important to fix but a 9.9? Nah

So if Cups is properly sandboxes this is less of an issue? Still not good but not show stopping
I don’t think this is 9.9 worthly

Good news, it’s not a 9.9. https://www.redhat.com/en/blog/red-hat-response-openprinting-cups-vulnerabilities

Remember when printers were connected by a USB cable?
Also,
sudo ss -tunlpto see what ports are listening on your system and which applications/services use them. (Linux)ss -Kcloses dead portsIf you didn’t explicitly open a port, ask why it needs to be open (listening). (25, 22, 67, 53,5353)
Make sure what you did open is opened at the right addresses. Ie localhost, 0.0.0.0, 127.0.0.1, etc for the purpose.
Use a firewall and block ALL incoming traffic.
Looks like a number of patches are landing in Ubuntu to address this: https://bugs.launchpad.net/ubuntu/+source/cups/+bug/2082335
Update: CUPS Remote Code Execution Vulnerability Fix Available

Cups-browsed-eez nutz!


