Why do so many companies and people say that your password has to be so long and complicated, just to have restrictions?
I am in the process of changing some passwords (I have peen pwnd and it’s the password I use for use-less-er sites) and suddenly they say “password may contain a maximum of 15 characters“… I mean, 15 is long but it’s nothing for a password manager.
And then there’s the problem with special characters like äàáâæãåā ñ ī o ė ß ÿ ç just to name a few, or some even won’t let you type a [space] in them. Why is that? Is it bad programming? Or just a symptom of copy-pasta?

Is it bad programming?
With very few exceptions, yes. There should be no restrictions on characters used/length of password (within reason) if you’re storing passwords correctly.

Underappreciated fact: Bcrypt has a maximum of 72 bytes. It’ll truncate passwords longer than that. Remember that UTF8 encoding of special characters can easily take more than one byte.
That said, this is rarely a problem in practice, except for some very long passphrases.

Bcrypt has a maximum of 72 bytes. It’ll truncate passwords longer than that. Remember that UTF8 encoding of special characters can easily take more than one byte.
Interesting: https://en.wikipedia.org/wiki/Bcrypt#Maximum_password_length
In the worst case a password is limited to 18 characters, when every character requires 4 bytes of UTF-8 encoding. For example: 𐑜𐑝𐑟𐑥𐑷𐑻𐑽𐑾𐑿𐑿𐑰𐑩𐑛𐑙𐑘𐑙𐑒𐑔 (18 characters, 72 bytes)Makes me question if bcrypt deserves to be widely used. Is there really no superior alternative?

Not only that, bcrypt could be run by GPUs and FPGA, that makes it more prone to bruteforcing attacks.
There are 2 modern alternatives: scrypt and argon2. They both require a substantial amount of memory, so gpu and hardware computation is no longer feasible.

And then there are times you set a password and everything just seems to work fine, but later the new password never works. You reset the password, try again and really focus because you think you made some mistake with the password manager. Again the password you set does not work.
You begin to google the problem and see that there is a max password lenght of 12. But you always set passwords of the lenght 20-30 and the interface never complained. But because you are desperate, you try just the first 12 characters of the last password you set. And it works!
I hate HP printers.
This explains a whole lot…

Old Steam calling.
Website and Client used different password rules, what worked for the other didn’t in the other.
Every time I find a site like this, I assume the programming is bad and the security is poor. (They don’t know how to sanitize input? They don’t know how to hash passwords?) It’s a good reason to use random passwords on every site for when that one is compromised.

What is “funny” is that I had the maximum password size thing on several bank websites (and a low one, at that). Fortunately, with 2FA, it doesn’t really matter I guess.

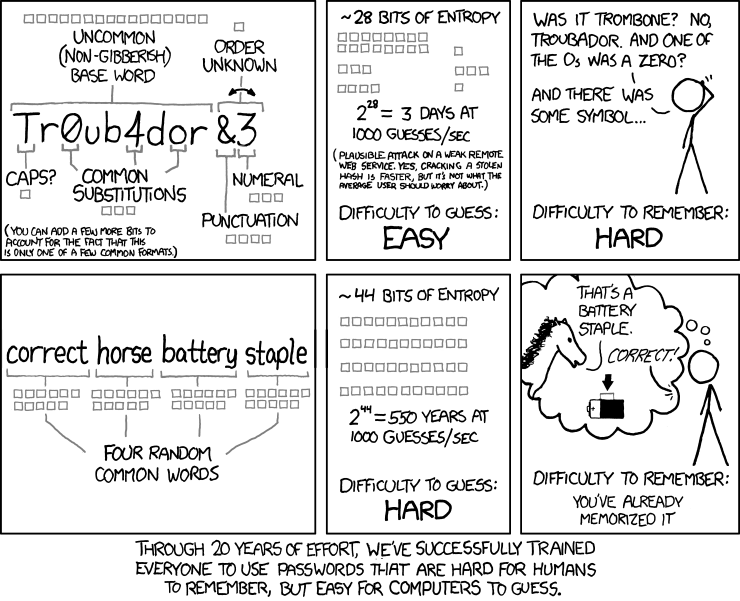
The new NIST guidance is to have something long. Special characters don’t matter. So a good passphrase that you can remember > short line noise. NIST also recommends against constant password rotation, but to instead audit for dictionary attacks. See also: https://www.netsec.news/summary-of-the-nist-password-recommendations-for-2021/
Yes, it is bad programming. Of course, on the backend you must never store passwords in the clear. You should never grow your own hashing algorithm.

Yes its bad programing. These restrictions suggest that the company is either doing improper storage and processing, or does not understand how to deal with passwords.
The proper password storage is a hash. This is a cryptographic function that is easy to do and imbossible to undo. The hash function operates on the underlying binary representation of your password, and doesn’t card what letters or symbols are in it. A program should take your password, hash it, and compare the result to the hash they have in their detebase.
The current recomended hash algorythm is called ‘bcrypt’. Depending on the implementation, the input is between 50 and 70 bytes (the spec was a little unclear so people defined the inputs diferently, but the algorithe is the same). This means a password should be able to take at least 50 normal keyboard characters, including letters, symbols, and spaces. Anything less than that indicates a poor practice on behalf of the website.
(a lot of this is simplified. There is some variation and nuance that I don’t think affects the main idea)

What about Argon2id? What are the advantages of bcrypt?

I don’t really know the strong points of either, I’m not a cryptographer. Bcrypt gets recommended because its relatively fast, its decent, and most importantly its already in most environments

Bcrypt is slow on purpose; all these methods are. More importantly, though, bcrypt is very well studied. Scrypt and argon2 had to catch up, but should be fine at this point.

Argon2 is the best (secure) crypto currently.
That said, adoption is slow, Bitwarden only recently implemented it for example.
That said, due to Argon2 being security-oriented, the recommended settings for it are pretty heavy.

Banks are the worst in this, the one website that should have secure passwords uses standards so low that KeePass can’t even go so low. I have to use a password I can remember, which may not actually be of a low standard but is in this case, considering it’s only 10 chars.

Banks are the single industry most likely to be handing the passwords over to a 1970s mainframe that expects everything to be encoded in EBCDIC at some point in the validation sequence.
This is an explanation, not an excuse.
That’s the digital equivalent to the key under the rock, but it’s the only rock on your porch.

I hope you’re using a password manager, I recommend bit warden if not.
Password requirements are all attempts at getting people to introduce entropy into their passwords. The length the characters the not allowed characters the allowed characters. All about adding entropy
Restrictions on allowed characters tend to be based on legacy systems and the input state allow. So if you have an input system that only has Latin characters, it would be foolish to allow non-Latin characters into a password, because then people could get stuck unable to login. So typically they reduce to the safest set of characters that all of their systems use. And for some of the older systems that parse passwords, some of the Meta characters could be problematic.
Password length is also down to legacy systems. If you have an old school Solaris system somewhere in your back end, that truncates password fields at 15 characters. Then 15 characters is the max.

Speaking of Password Managers, PLEASE DO NOT FORGET THAT PASSWORD.
Because that’s gonna be a bit annoying [Very Annoying].
My story: https://reddthat.com/post/1115518
😟

While most of the time, I remember my password, I know I could just snap and forget it right there at any point. Happened to me not once. And I’m in my 20s. Sometimes when I forget a password, I just start typing and muscle memory kicks in, sometimes it doesn’t. I guess our brains are not optimized to store long random strings of characters. You could use a long sentence as your master password or do as I do:
Come up with a way to make up a long seemingly random password from a couple words. Then if/when you forget a password, just remember those words and reconstruct password from them.
- Don’t use common dictionary words or anything from popular media, as it could be guessed by attackers.
- You can write down algorithm on a piece of paper and keep it somewhere safe.
- Words should be related but not directly:
- two asteroid names - bad
- asteroid name and it’s greek translation - bad
- real city name and city name from a book - good
- two words that both start with S and end with T - good
- If you forget both words, you should be able to remember/look up at least one of them if you still remember how you came up with the word.

I used a passphrase generated from a word, kinda like an acrostic poem.
Exmaple: LEMMY
Lemonade Endeavor Makes Melons Yellow
I know the word that I used to generate my passphrase, I’m just missing one word of the passphrase, but I know the starting letter.
I could theoretically “brute force” all the words that starts with that letter, but I’m just too depressed and unmotivated to solve a captcha for each guess. Maybe I’ll find the missing word, but it could take months.

It feels like a lot of sites are taking active measures to block the use is password managers, too. I hate those sites. Why I’m the hell would you do that???

Example please? This has not been my experience

Prairie Centre Credit Union.
After years of complaining, they finally did something about their hopelessly insecure authentication, only to completely bork it.
Bitwarden could open the site, but couldn’t push the login info. They prohibited pasting, so I had type everything by hand. And they couldn’t even get that prohibition right, because I discovered that I could type a character then CTRL+V to paste, then HOME, DEL.
All of that is written past tense, because it was the last straw. I took my banking elsewhere, despite the fact I now have to drive 2.5 hours if I need to talk to someone in person.

Mainly financial sites, in my experience. I also have problems logging into Mastodon, because if I manually type my user and password I get logged in but if I use Bitwarden or even copy/paste it fails.
But also every site where you type in the user name and then submit and it takes you to enter the password - I use a lot of custom emails to avoid spam so I may not remember my username for a given site, but Bitwarden won’t recognize it as a login page (much bigger problem on mobile, which is where I do most of my stuff).

It’s your browser. You can install JavaScript or a browser extension which disallows the no paste input field. So that you can always paste in.
The financial institutions that implement that they’re trying to guard against local copy and paste password theft. Any program can have access to the clipboard. So I understand why they do it, and I understand why it’s annoying.
For financial institutions I highly recommend using something like a Fido 2 key. I’m partial to the yubikey bioseries.

BitWarden seems a little dumber at detecting password update submissions than LastPass. Same with detecting when there’s a login field on a page. Really, webdevs should do the most simple-stupid thing and give those fields predictable names like “old_password”/“new_password”/“new_password_retype”. No reason to get creative here.
That’s about it. I switched out of LastPass for a reason and I’m not going back.

Bitwarden F-Droid repo

Is it bad programming
No, it’s bad requirements, well ok maybe the programmer came up with the requirements too.

Non-ASCII characters can cause troubles because of different encodings and because you may need to type them on a machine where corresponding keyboard layout is missing.
The password length limit is nothing short of stupid.
My mother’s password for everything got compromised recently. I told her to think of a sentence that will never happen and to write it down and store it somewhere safe.
She remembered it instantly.
Oh, and I made her a password manager

Likely more bad design than bad programming, but that’s not a very meaningful distinction.
It’s downright scary how many “professionals” are onboard with this shit.

Some of the restrictions are there to try and protect users from themselves. Most people don’t want to put a space in their password so it’s assumed it was a mistake when they do.

I always thought banks (of all places) had the most ridiculous requirements. What, a 5 character pin to get read access to most of my financial data? Are you kidding me? That’s like securing your bike with a numbers lock
