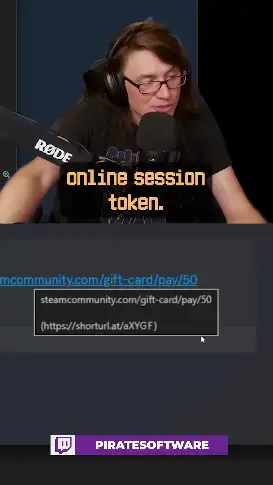

Typically, with scams like this, the attacker is using a tool like Evilginx.
The way this works is that Evilginx runs on a server that the hacker controls and will request the login page from whatever service they are targeting(Discord, Steam, Google, etc) and then serve it to you as a proxy. It looks entirely legitimate unless you make sure to very closely check the URL.
Once you login, it will take a copy of your Username, your password, and your session token(the thing that lets Discord know it’s you so you don’t need to login again after every refresh). and suddenly the attackers now have access to your account to do whatever they want with it.
Discord should absolutely prevent modifying links in this way specifically for this reason, but good practice as a user is to hover over every link and make sure it’s pointing where it’s supposed to. Don’t click on anything that looks suspicious.

Does this rely on the user typing in their password, or does somehow even the browser fall for it and autofill it?
Because in that case, to respond to OP: Firefox is not vulnerable to this, but most users themselves are. Using a password manager like Bitwarden would help, because if you add the website’s real URL to your password entey (happens automatically for the current URL at password entry creation), bitwarden will simply just not show your password entry when the URL does not match.
Also, install uBlock Origin and turn on it’s phising blocklists in the settings. It can be helpful.

An attack using this tool does require that the user actually logs in, but because they’re just acting as a proxy for the real login page, the only way you’d spot the difference is if the URL doesn’t match (or that your password manager doesn’t auto-fill)
However, it’s pretty easy to see that someone would be fooled by that as you’d expect to need to confirm your identity when adding a gift card to your steam account.
I don’t understand, as you said the hacker’s server requests my credits, so am I not supposed to be prompted to accept something by the browser or Discord app? Twitter and Google usually prompt you and require you to click “allow”

You’ve got half of it. The hacker’s server is acting as a middleman for the real login page. Everything appears legitimate except the URL will be wrong and if you use a password manager, it won’t auto-fill
They access the legit login page and forward it to you, but they’re in the middle capturing everything you send.
When you enter your login details, they will record them and then forward them to the real login window in near real time, effectively logging in as you. They then have a legitimate session token which they can use to access your account without needing to re-authenticate.
aah, so in this trick I have to enter my creditentials again,

Hacking Discord is easier than anything else because every account has a passcode that you can easily obtain using regular social engineering or remote access and it bypasses everything, even 2FA.

What passcode? Are you referring to recovery codes?

Idk anything about any recovery codes. I was referring to a thing that’s called something like “security token”.

Ah, alright. Like an API key.

No it’s not an API key. It’s changed every time you change your password so it’s basically an alternative one but it has an additional feature of bypassing 2FA.

TL;DR: No.
You won’t get hack by only clicking on this link (except if their is a critical exploit in your browser which makes it possible).
phew

Someone in the comments raised a good question: how clicking a link to a third party website, exposes a discord auth token?
so, he just over-exaggerated things here, actually when you click there is a page that asks you for your creditentials and kids get tricked to enter them

So really it’s a phishing attack? Maybe he should say that instead instead of being an alarmist that clicking a link will get your credentials stolen.
Every video I see of this guy is filled with disingenuous bs.
hmm yeah most likely. I forgot to add a question mark at the end of my reply, maybe it’s not the case, maybe

that steals your discord auth token
How???
that steals your discord auth token
the general census on this thread is that he war over-exaggerating, he meant that it tricks you into inserting you Credential

So this is just “HTML link hiding in emails” but all over again?

